4月15日-在白宮週四一份聲明 中稱,俄羅斯對外情報局(Sluzhba Vneshney Razvedki,SVR)要為SolarWinds事件負責。該事件導致九家聯邦機構和數百家私營企業數據外洩。白宮的新聞稿證實了過去的媒體報導,俄羅斯對外情報局SVR是SolarWinds事件的幕後黑手,正式指責SVR通過其部門的特工駭客(通常稱為APT29,The Dukes或Cozy Bear) 開展廣泛的網路間諜活動。
通過破壞SolarWinds供應鏈,SVR存取全球超過16,000台電腦,能監視或潛在破壞那些電腦,多個美國政府機構是這場廣泛的網路間諜活動的受害者,國務院,司法部,能源部,網路安全和基礎設施局以及財政部是披露被入侵的最大機構。資安公司如FireEye,Malwarebytes,Microsoft,Mimecast等也是針對特定目標。白宮的摘要指出:“美國情報界對SVR的歸因評估充滿高度信心。” 根據美國政府的說法,這種入侵的範圍涉及國家安全和公共安全。而且給大多數私營機構的受害者帶來了不適當的負擔,俄羅斯須承擔這一事件的異常高昂的代價。
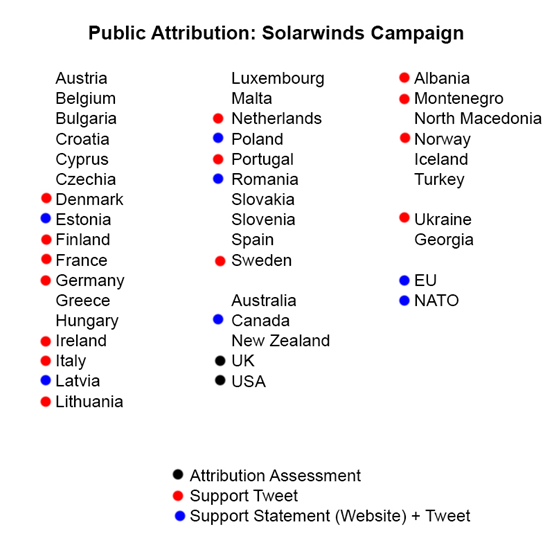
目前許多政府已經出來支持美國對SolarWinds的歸因評估。英國也同時發布了歸因評估目前,14個國家政府在其官方網站上發布了支持性推文,另有7個發布了支持性書面聲明和推文。
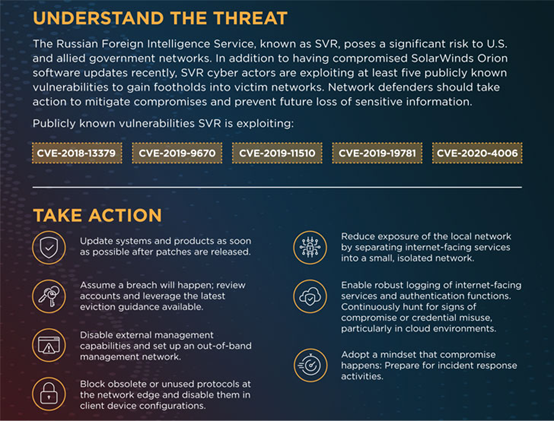
此外,國家安全局(NSA),網路安全和基礎設施安全局(CISA)和聯邦調查局(FBI)共同發布了一份諮詢報告 ,警告企業SVR積極利用五個已知的漏洞進行初步攻擊立足於受害設備和網路:
CVE-2018-13379 -Fortinet FortiGate VPN
CVE-2019-9670 – Synacor Zimbra Collaboration Suite
CVE-2019-11510 – Pulse Secure Pulse Connect Secure VPN
CVE-2019-19781 – Citrix Application Delivery Controller and Gateway
CVE-2020-4006 – VMware Workspace ONE Access
企業應注意該警告,並採取必要的步驟來識別和防禦SVR進行的惡意活動。
根據拜登總統今天發布的行政命令,美國財政部 對以下俄羅斯科技公司已實施制裁,六家科技公司被指控幫助SVR,俄羅斯聯邦安全局(FSB)和俄羅斯主要情報局(GRU)對美國進行惡意網路活動。
被制裁的六家科技公司或機構包括:
ERA Technopolis –由俄羅斯國防部資助和運營的研究中心和技術園區。ERA Technopolis擁有並支持俄羅斯主要情報局(GRU),負責進攻性網路和資訊作戰,並利用俄羅斯技術部門的人員和專業知識來開發軍事和雙重用途技術。
Pasit –位於俄羅斯的IT公司,進行研究和開發以支持俄羅斯對外情報局服務(SVR)的惡意網路操作。
SVA –俄羅斯國有研究機構,專門研究位於俄羅斯的先進資訊安全系統,進行研究和開發,以支持SVR的惡意網路操作。
Neobit –位於俄羅斯聖彼得堡的IT安全公司,其客戶包括俄羅斯國防部,SVR和俄羅斯聯邦安全局(FSB)。Neobit進行研究和開發,以支持由FSB,GRU和SVR進行的網路運營。Neobit還根據與網路相關的EO 13694(經EO 13757,與WMD相關的EO 13382和由《打擊制裁的美國對手》(CAATSA)修訂)的指定,為GRU提供物質支援。
AST –俄羅斯IT安全公司,其客戶包括俄羅斯國防部,SVR和FSB。AST為FSB,GRU和SVR進行的網路運營提供了技術支持。AST還根據EO 13694,EO 13382和CAATSA被指定為FSB提供支援。
Positive Technologies –一家俄羅斯資安全公司,為包括FSB在內的俄羅斯政府客戶提供支援。Positive Technologies為俄羅斯企業,外國政府和國際公司提供電腦網路安全解決方案,並舉辦大型會議,這些會議被用作FSB和GRU的招募活動。Positive Technologies還根據EO 13694,EO 13382和CAATSA被指定為FSB提供支援。
值得注意的是,美國財政部的制裁名單還包括俄羅斯資安公司Positive Technologies,該公司以其在網路安全漏洞研究方面的工作而聞名全球。
美國公司和金融機構不再能夠與上述的公司或機構開展業務,除非獲得美國的外國資產管制處(Office of Foreign Assets Control,OFAC)申請的許可。
SolarWinds供應鏈攻擊的有關情資:
https://otx.alienvault.com/pulse/60413cd1bb43dcf1d22c274b
https://otx.alienvault.com/pulse/5fd6df943558e0b56eaf3da8
https://otx.alienvault.com/pulse/5fe0d2b1258adac64a4f9adc
https://otx.alienvault.com/pulse/5fd825b7fa4eb2223a0cf812
https://otx.alienvault.com/pulse/5ffc7929fdeee95e277473b7
https://otx.alienvault.com/pulse/5ffccc003adfeeafe1d401a8
https://otx.alienvault.com/pulse/5fdce61ef056eff2ce0a90de